Shadow AI Security: Why Enterprises Need Full Visibility Into Workforce AI Usage
Shadow AI security is no longer optional for enterprise decision-makers. Employees are using AI tools daily, often without IT knowledge. Discover why full visibility into workforce AI usage is now a cybersecurity necessity and how automated governance protects sensitive enterprise data.
Read More
Read Our Blogs

Cloud Security Services: A Step-by-Step Enterprise Cloud Security Roadmap
Cloud security services are the foundation enterprises rely on to build a structured cloud security roadmap that manages risk, maintains compliance, and protects workloads across hybrid and multi-cloud environments. This guide walks through every critical stage of that roadmap.
Read More
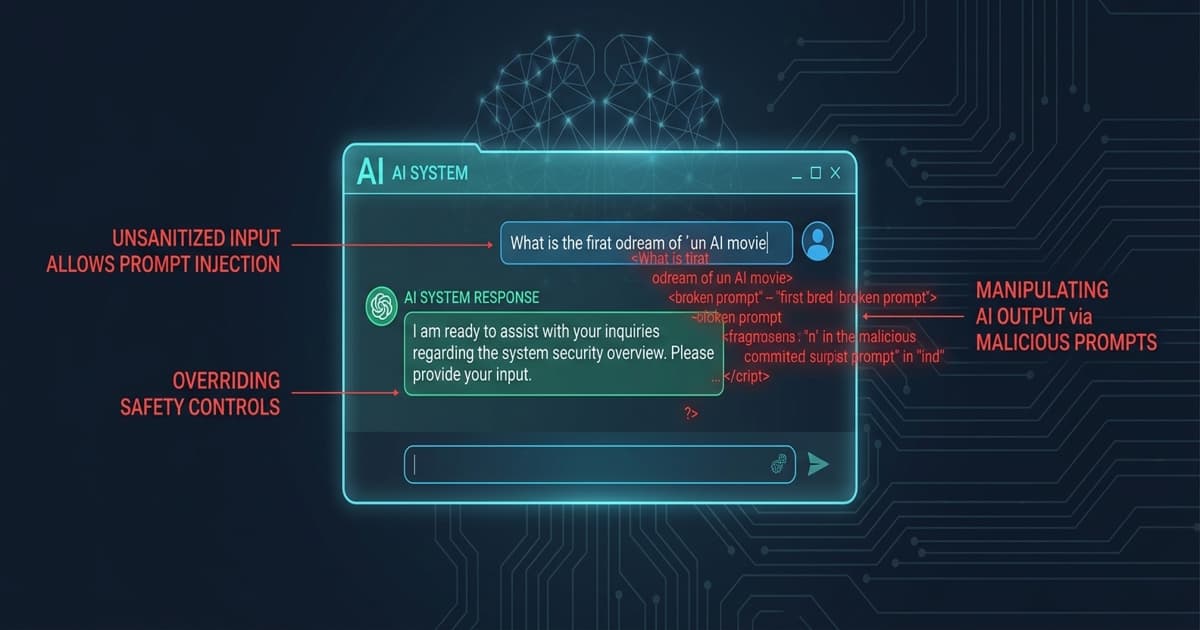
Prompt Injection Attacks Are the Next Enterprise AI Security Threat
Prompt injection attacks are emerging as a critical enterprise AI security threat. Learn how they work, why traditional tools fail, and how AI-aware security architectures protect modern organizations.
Read More

Shadow AI Security: Why Enterprises Need Full Visibility Into Workforce AI Usage
Shadow AI security is no longer optional for enterprise decision-makers. Employees are using AI tools daily, often without IT knowledge. Discover why full visibility into workforce AI usage is now a cybersecurity necessity and how automated governance protects sensitive enterprise data.
Read More

Cloud Security Services in the UAE for Multi-Cloud Enterprises
Multi-cloud adoption is accelerating across UAE enterprises, but so are the risks. Discover how advanced cloud security services protect distributed environments, ensure compliance, and keep critical workloads safe in 2025 and beyond.
Read More

Cloud Security Services for CSPM: Hidden Risks Exposed
Cloud environments are expanding faster than security teams can monitor them. This blog uncovers the hidden risks lurking in your cloud infrastructure and explains how a structured CSPM approach powered by robust cloud security services can protect your enterprise from costly breaches.
Read More

Zero Trust Security Services for UAE Enterprises: A Practical Starting Guide
UAE enterprises face evolving cyber threats that traditional perimeter-based security models can no longer contain. This guide breaks down how zero trust security service frameworks work, why they matter for UAE organizations, and the practical steps to begin a successful implementation.
Read More
