Hyper Converged Infrastructure and Servers
Modernize the data center, accelerate the path to hybrid cloud, and enable cloud native applications with HCI. System Software delivers highly differentiated features and benefits extending capabilities to automate deployments and ongoing operations while providing full stack single-click lifecycle management.

Virtualization
Power your computing environment for modern applications using any combination of virtual machines, containers and Kubernetes with VMware vSphere, the industry's leading server virtualization software.

Data Protection and Disaster Recovery
Protect Your Business Data and Applications. An integrated approach to data protection, ensuring that your critical data and applications can be recovered.

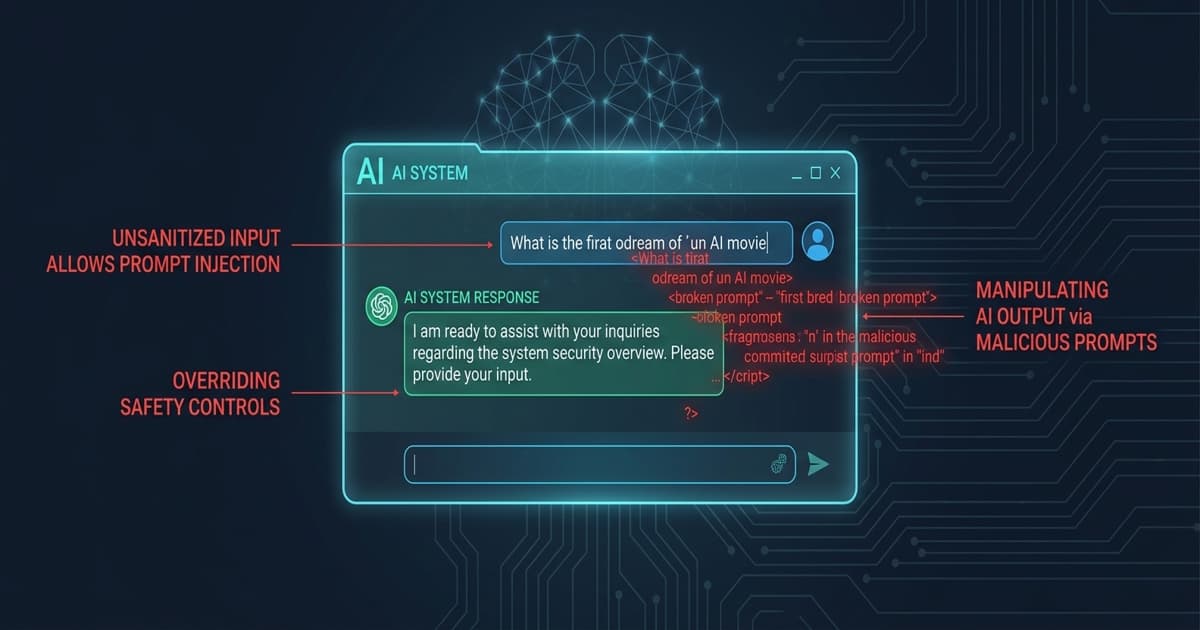
Security and Compliance
Gives you deep, unparalleled visibility into your security system state and security posture. Out-of-the-box platforms and policies enforce regulatory compliance standards

Storage Infrastructure
Get the scalability, intelligence, and cloud integration you need to unlock the value of your data. Accelerate your critical workloads from core to edge to cloud while decreasing application outages and reducing storage requirements with advanced deduplication

Network Infrastructure
Optimize your network by reaching users wherever they are, ensuring business continuity no matter what, and accelerating innovative capabilities when it matters most
Trends and Insights
AI & Cybersecurity Insights
Get in touch
Trust is our
foundation. Results
are our drive.
Great partnerships build better products. With deep expertise in QA and security, Unicorp is the team you need to scale your ambition and deliver flawless results with precision.
Contact UsNeed to discuss?
Let's make your next solution secure and high-performing.