Data Security
The purpose of digital infrastructure security is not to protect the infrastructure but to protect the data being stored, transmitted, and processed within that infrastructure.

Attack Surface Defense
Delivers proactive intelligence to disrupt phishing, impersonations, malicious domains and data leakage across the public, deep and dark web. Moreover, provides protection against the full range of threats at wire speed anywhere on your network.

Advanced Security
Web application firewalls provide businesses with a flexible and precise tool for fully securing applications against web attacks and zero-day exploits

Security and Compliance
Gives you deep, unparalleled visibility into your security system state and security posture. Out-of-the-box platforms and policies enforce regulatory compliance standards

Identity and Access Management
Identity and Access security is the easiest way to implement your digital transformation faster and reduce risk. Automate, manage, and govern access in real time, with AI-enhanced visibility and controls

Email and Endpoint Threat Protection
Email authentication is a necessary first step towards identifying the origin of messages,and thereby making policies and laws morenforceable. Protection offers advanced automated threat detection and response against an ever-growing variety of threats, including fileless and ransomware

Security Operations Monitoring and Auditing
Keeping up with the barrage of threats requires an open, comprehensive solution that provides deeper visibility, automation and contextual insights across endpoint, network, cloud, and applications while working with your existing tools.
Trends and Insights
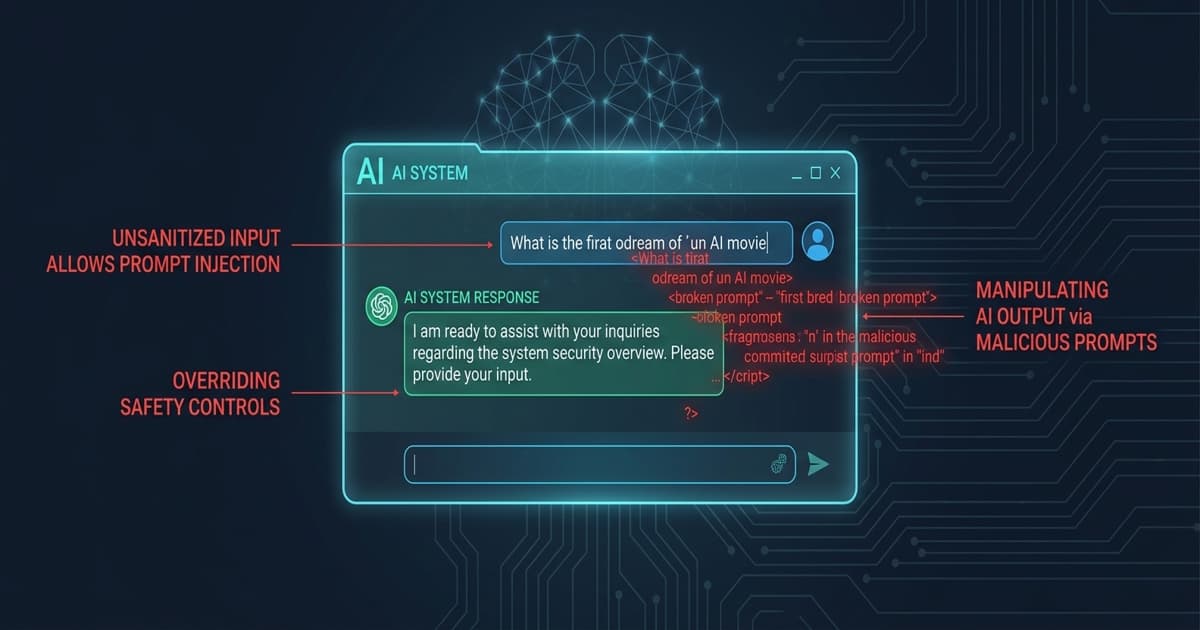
AI & Cybersecurity Insights
Get in touch
Trust is our
foundation. Results
are our drive.
Great partnerships build better products. With deep expertise in QA and security, Unicorp is the team you need to scale your ambition and deliver flawless results with precision.
Contact UsNeed to discuss?
Let's make your next solution secure and high-performing.